The basic concept
To find an introduction into the subject, it makes sense to look into the essential terms of connected driving firstly. There is a fundamental distinction between V2I and V2V.
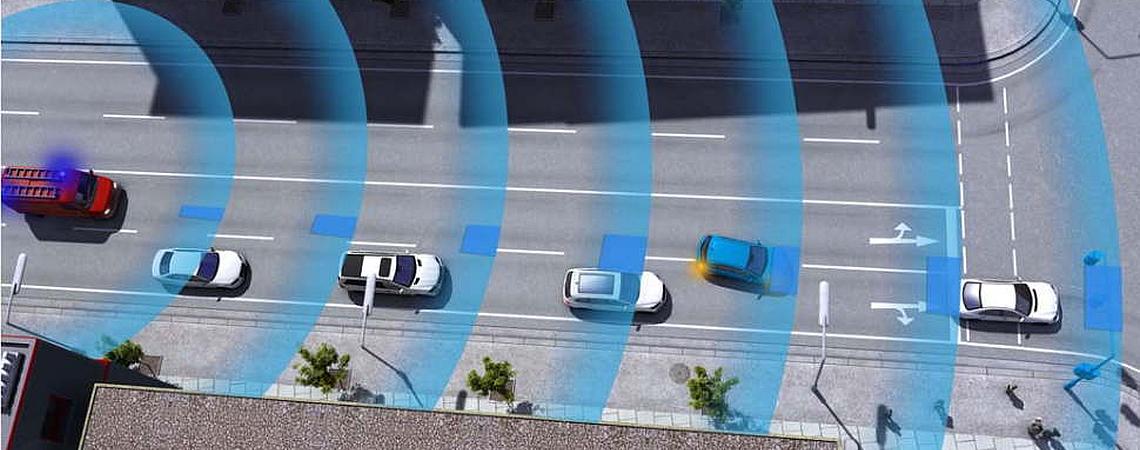
V2I (also called C2I) stands for Vehicle-to-Infrastructure. This describes the communication between a vehicle and the infrastructure. In this case, infrastructure means facilities in or nearby the streets, for example in traffic lights or in the concrete, gathering global and local data concerning the traffic and the road conditions. This data can then lead to the infrastructure suggesting a certain behavior to vehicles in a defined area or even forcing it on them.
For example, it would be possible to recommend the speed, acceleration and distance to other vehicles based on the current traffic conditions. This serves the purpose of optimizing pollutant emissions, fuel consumption and the pace of the traffic in general.
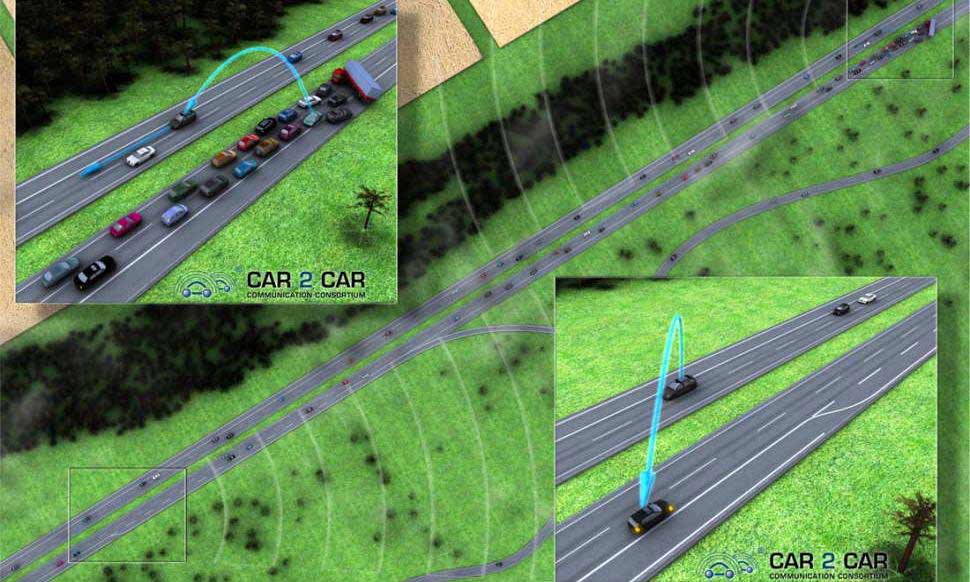
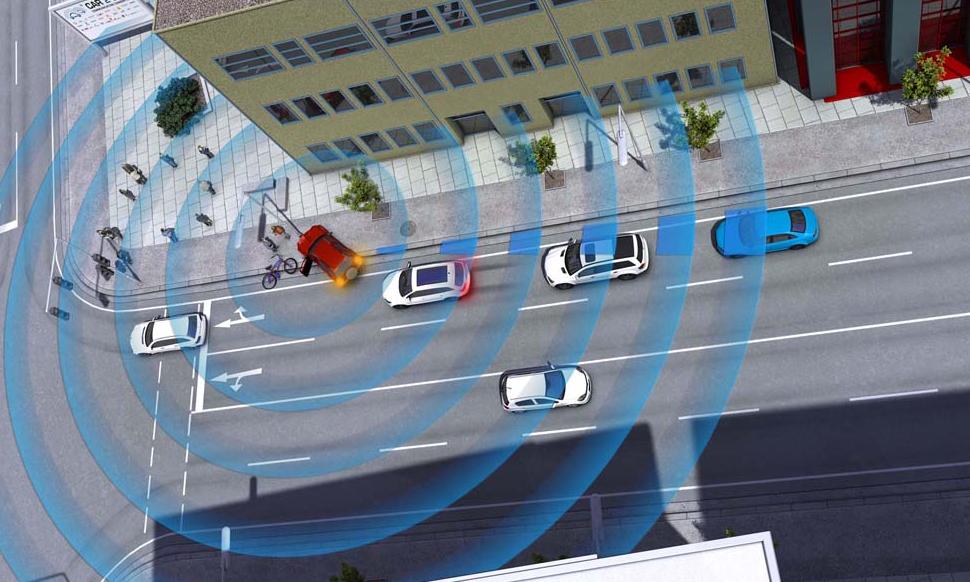
The second important term is V2V (also called C2C), meaning Vehicle-to-Vehicle. This refers to the communication of vehicles among each other. Theoretically, this should work as follows: if two or more cars or street facilities are in range for communication, they establish an Ad-hoc network (Vehicular Ad Hoc Network VANET) which allows for sharing the position, speed and direction of travel of the vehicles. Each vehicle can be seen as a router that can be used to send messages to even more distant vehicles.
V2V is more difficult to implement as the structure is very decentralized. This means that every car has to feature the appropriate technology, not only the infrastructure of the streets. Furthermore, V2V is reliant on the collaboration of different car manufacturers and suppliers concerning communication technology, protocols and so on.
For such a system to function properly, security technology is needed locally as well as on higher levels. The system has to be able to take automatic and semi-automatic decisions to express warnings or to eventually influence the manner of driving of the vehicle directly. Insecurities, delays in the evaluation of data as well as security issues have to be constantly taken in account while doing so.